The Digital Operational Resilience Act, widely known as DORA, represents a landmark shift in how the European Union oversees the financial sector's relationship with technology. Applied since January 17, 2025, this regulation moves beyond traditional financial capital requirements to focus on the technical and operational stability of the entire financial ecosystem. It assumes that a single IT failure in a major institution could trigger a systemic crisis across the European economy. For organizations to achieve compliance, they must navigate a rigorous set of requirements distributed across five foundational pillars.
The Five Pillars of Digital Operational Resilience
The core of DORA comprises five thematic areas that define the necessary capabilities for a modern financial entity. The following table summarizes these pillars and their primary objectives.
| Pillar | Relevant Articles | Primary Objective |
|---|---|---|
| ICT Risk Management | Articles 5 to 16 | Establishing a proactive framework to identify, assess, and mitigate digital risks. |
| Incident Management & Reporting | Articles 17 to 23 | Streamlining how major ICT incidents are classified and reported to authorities. |
| Digital Resilience Testing | Articles 24 to 27 | Regularly verifying the effectiveness of security measures through technical assessments. |
| Third-Party Risk Management | Articles 28 to 44 | Managing the risks arising from a heavy reliance on external ICT service providers. |
| Information Sharing | Article 45 | Encouraging voluntary collaboration on cyber threat intelligence within the industry. |
Core Principles and Their Implications
1. Management Body Responsibility
DORA makes the board of directors and senior management explicitly responsible for the entity's digital operational resilience. This implies that compliance is no longer just a task for the IT department but a strategic priority for the C-suite. Management must approve the risk framework, set the risk tolerance for ICT issues, and allocate an appropriate budget for security training and infrastructure. To comply, board members must undergo regular, specific training to maintain the skills needed to understand and assess ICT risks effectively.
2. Comprehensive ICT Risk Management
Organizations must maintain a documented framework that covers all physical infrastructures, hardware, and software assets. This principle implies that every business function must be mapped to the technology supporting it. Working toward compliance requires maintaining a complete inventory of assets and identifying "critical or important functions" that could impact the entity’s stability if disrupted.
3. Strict Incident Reporting Windows
One of the most demanding principles involves the rapid notification of major incidents to competent authorities. For major events, the initial warning deadline is often as short as 4 hours, which is significantly stricter than other regulations like NIS2. This implies that manual reporting processes are often insufficient. Organizations should invest in automated monitoring and alert mechanisms to ensure timely detection and communication.
4. Rigorous Resilience Testing
All entities must conduct basic resilience testing, such as vulnerability scans and network security assessments, at least once a year. Larger, systemically important institutions are further required to perform advanced Threat-Led Penetration Testing (TLPT) every three years. This involves a red team conducting a simulated stealth attack on live production systems to test defensive capabilities.
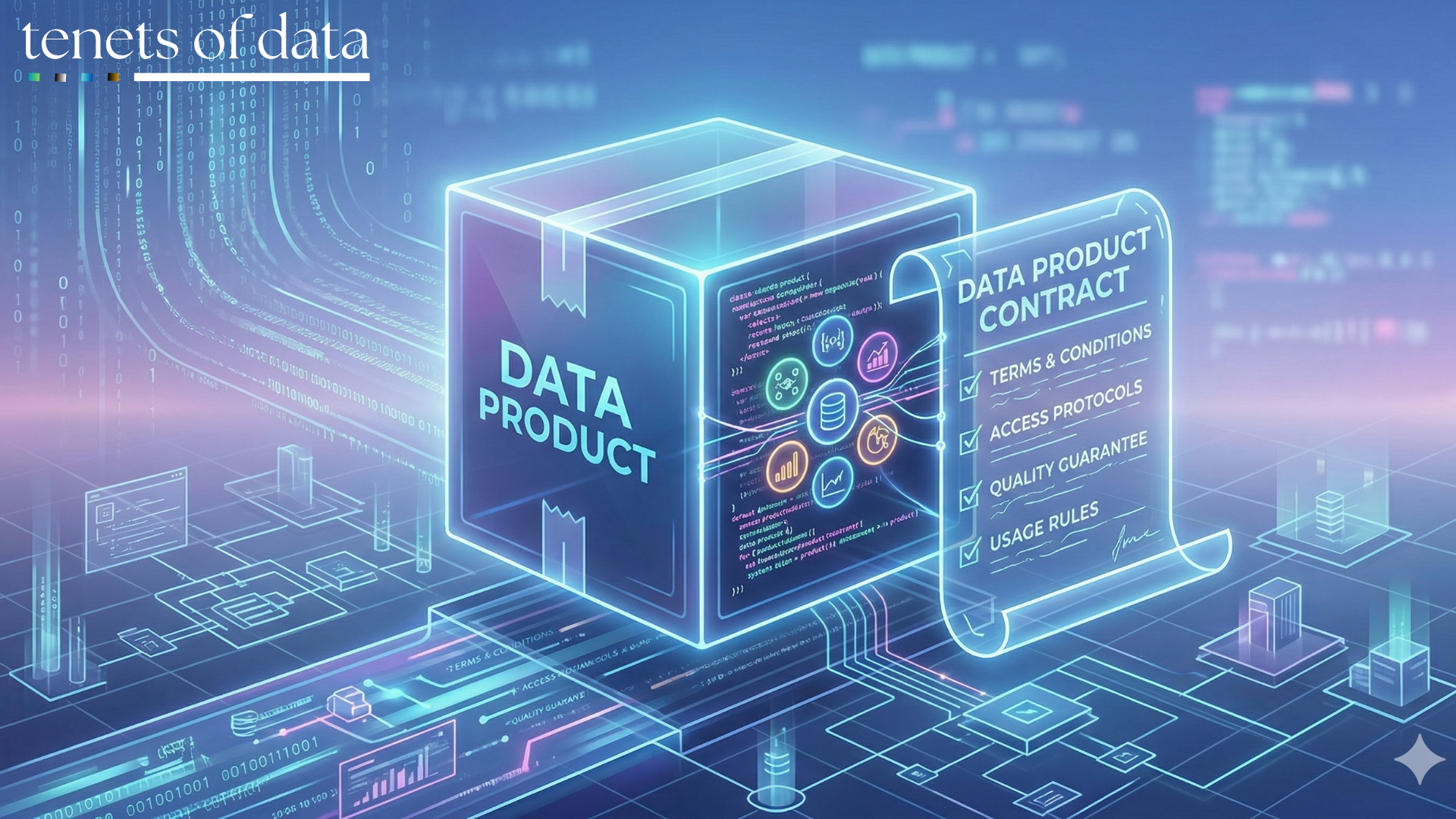
5. Strategic Third-Party Oversight
Because financial firms are heavily dependent on cloud and software providers, they must maintain a Register of Information on all contractual arrangements. This implies that firms must conduct thorough due diligence before signing contracts and ensure their agreements include mandatory DORA clauses, such as unrestricted audit rights and clear exit strategies.
The Process for Achieving Compliance
Organizations should follow a structured lifecycle to align their operations with DORA mandates.
- Conduct a Scope and Gap Analysis: Determine whether the organization falls within the 20 categories of financial entities or serves as a critical ICT third-party provider. Compare the current security posture against the requirements in Articles 5 through 15.
- Define Critical or Important Functions (CIF): Formally identify which business services are essential. This step is vital because CIFs attract much higher standards for testing and vendor management.
- Formalize Data and ICT Inventories: Map all hardware, software, and data assets to the business units they support. Establish technical data lineage to understand how information flows through the system.
- Renegotiate Third-Party Contracts: Review existing agreements with ICT providers to ensure they include the provisions required by Article 30. This process often takes significant time for large enterprise agreements.
- Build an Incident Response Playbook: Create a crisis communication strategy that accounts for the short reporting windows mandated by the regulation. Assign clear roles and responsibilities for incident management.
- Implement a Continuous Testing Program: Schedule annual assessments for critical systems. If the entity is likely to be identified for TLPT, begin selecting accredited red team and threat intelligence providers.
- Establish Board Oversight and Training: Set up regular reporting channels to the board and implement a training program for senior leadership to ensure they can fulfill their legal obligations.
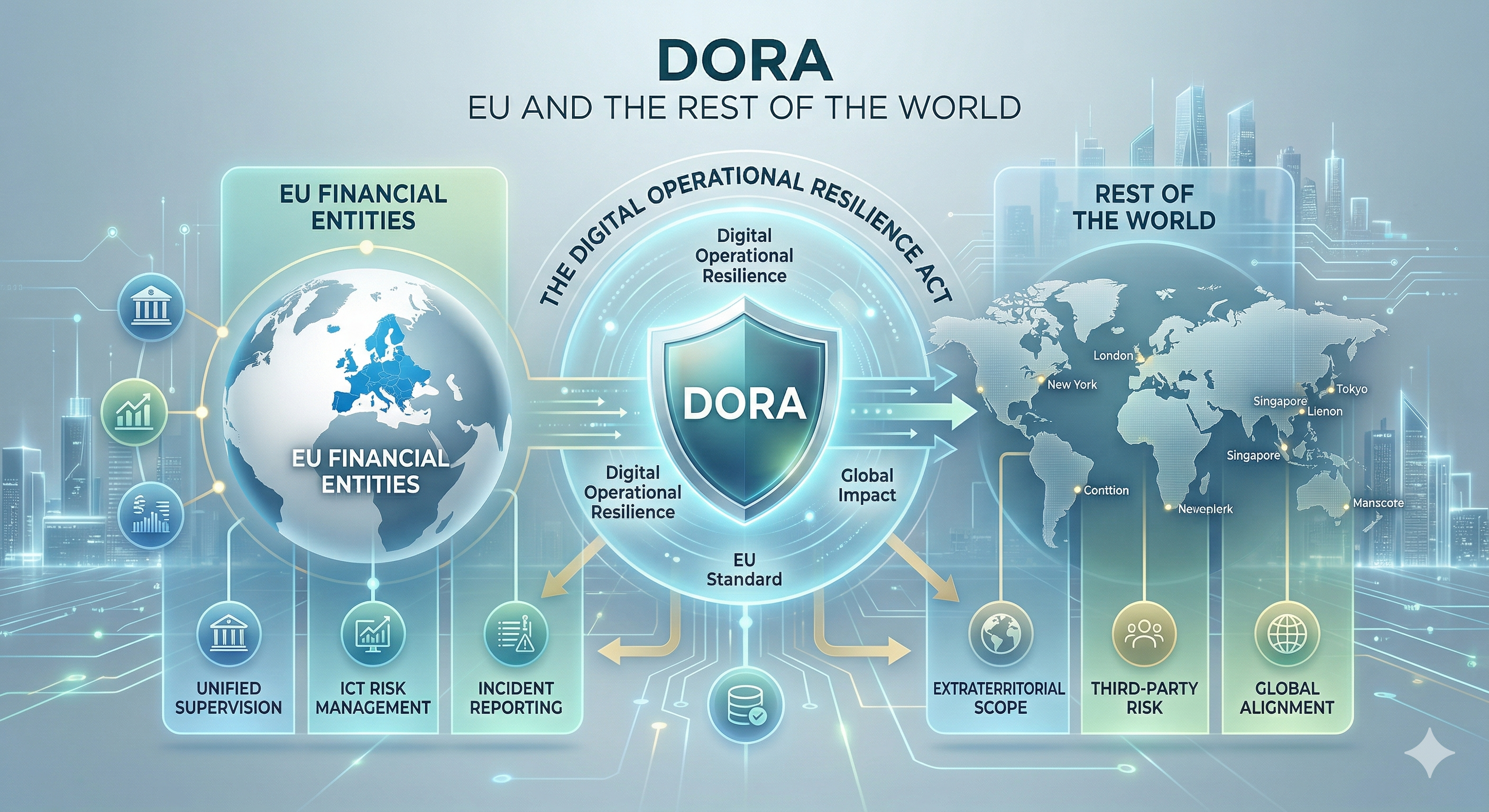
Impact on Organizations Outside the EU
DORA has significant extraterritorial reach, affecting organizations globally.
- Service Delivery Jurisdiction: Any non-EU ICT service provider that delivers services to financial institutions operating within the EU must comply with DORA requirements. Jurisdiction is determined by where the services are delivered rather than where the provider is established.
- Direct Oversight of Critical Providers: Major non-EU technology firms, such as cloud providers, can be designated as "critical ICT third-party service providers" at the Union level. This designation brings them under the direct supervision of European Lead Overseers, such as the European Banking Authority.
- Contractual Flow-Down: EU-based financial entities are prohibited from using ICT providers that do not meet the security and resilience standards defined in DORA. This forces non-EU vendors to adapt their internal controls and contractual terms if they wish to continue serving the European financial market.
- Audit and Inspection Rights: Non-EU providers must often grant European regulators and their clients unrestricted access and inspection rights to their premises, even if those facilities are located outside the Union.
Failure to comply can result in severe financial penalties. For financial enterprises, fines can reach up to 2% of annual global revenues, while critical third-party providers can face daily penalty payments for up to six months until compliance is achieved.